As artificial intelligence (AI) rapidly integrates into financial technologies, its use in the crypto industry is expanding — from trading bots and portfolio management tools to customer service and security systems. However, experts warn that AI agents may introduce an entirely new class of vulnerabilities, and the crypto sector may not be prepared.
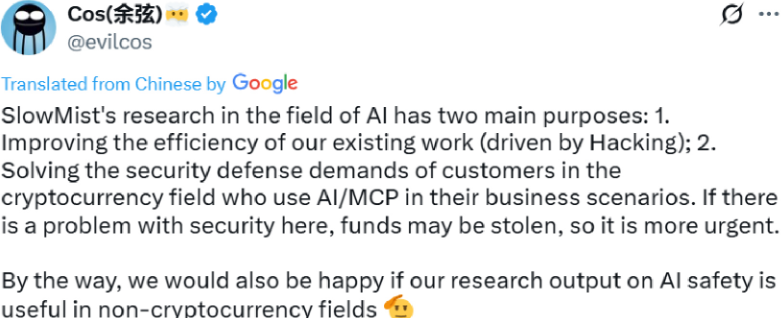
AI integration is outpacing security innovation, creating potential blind spots that malicious actors could exploit.
Crypto’s Growing Reliance on AI Agents
Over the past year, crypto platforms and decentralized applications (dApps) have increasingly adopted AI-powered agents to streamline operations. These agents can automate trading, detect fraud, analyze market sentiment, and even interact with smart contracts in real time.
AI agents now make decisions at high speed, sometimes with limited oversight — a setup that opens the door to potential exploits.
Projects like Autonolas, Fetch.ai, and Ocean Protocol are pushing the boundaries of AI autonomy within Web3 ecosystems, but the security frameworks around these systems remain immature.
AI has a trust problem — Decentralized privacy-preserving tech can fix it
Unseen Vulnerabilities in Complex Systems
AI models, especially large language models (LLMs) and machine learning agents, are often considered black boxes. Unlike traditional smart contracts with transparent codebases, AI agents can behave unpredictably when exposed to adversarial data or edge cases.
An AI trading bot could be manipulated through coordinated false signals or market noise. Worse, it might trigger self-reinforcing losses without realizing it.
Moreover, prompt injection attacks, data poisoning, and model manipulation are now being studied as viable threats — and the crypto industry may become a prime testing ground.
Smart Contracts + AI: A Dangerous Combo?
Combining AI agents with smart contracts increases automation but also compounds risks. If a malicious actor can exploit the AI layer, they may be able to trigger smart contract actions without traditional vulnerabilities being present in the contract code itself.
The fusion of deterministic blockchain systems with non-deterministic AI behavior creates an unpredictable attack surface.
This is particularly concerning in DeFi, where financial logic is immutable and self-executing — meaning a flawed AI-triggered transaction might be irreversible.
Conclusion: Prepare Before It’s Too Late
AI agents bring massive potential to crypto — but they also carry hidden risks the industry is not ready for.
Without rigorous testing, AI-specific security audits, and cross-domain expertise, the next wave of crypto exploits may not come from traditional bugs — but from intelligent systems behaving badly.
The call is clear: the crypto industry must secure its AI layer before the vulnerabilities secure them.

