A leading blockchain security firm has released its comprehensive post-mortem report on the Cetus decentralized exchange (DEX) hack, shedding new light on how attackers were able to steal $223 million in user funds.
This major breach is now one of the largest DEX exploits of 2025, raising serious concerns about security practices across DeFi platforms.
What Happened During the Cetus Hack?
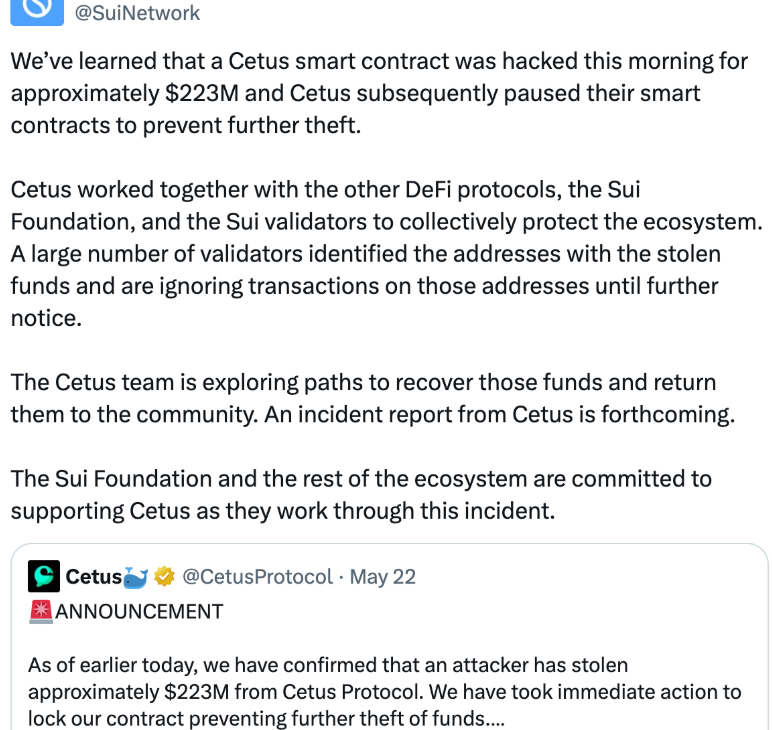
The exploit occurred in mid-May 2025 and involved a smart contract vulnerability that allowed the attackers to bypass trading restrictions and drain funds from liquidity pools.
“An integer overflow bug in the contract logic allowed the attacker to manipulate pool pricing and execute unauthorized withdrawals,” the report states.
Cetus, a prominent exchange built on the Sui blockchain, initially reported the breach after users noticed abnormal slippage and disappearing balances.
$223 Million Stolen — But Most Funds Frozen
According to the security firm’s analysis, the attacker siphoned over $223 million in tokens, including SUI, USDC, and CETUS-native assets. However, thanks to swift coordination with Sui network validators and ecosystem partners, a majority of the stolen funds have been frozen.
“Approximately $186 million has been locked in flagged wallets across centralized and decentralized endpoints,” the report confirms.
This rapid response has been praised by the crypto community as a model for coordinated emergency actions in DeFi.
Post-Mortem Recommendations
The post-mortem outlines key technical recommendations for other DEXs and developers:
- Implement rigorous unit testing for all arithmetic functions in smart contracts.
- Adopt automated fuzzing tools to simulate edge-case attacks.
- Enforce multi-layer verification before contract deployment.
- Ensure real-time monitoring of unusual pool activity.
“This incident was avoidable with basic safety mechanisms and code auditing,” the report states bluntly.
Cetus and Sui Respond to Crisis
In response, Cetus has temporarily suspended all trading activity and is collaborating with Sui and third-party investigators to recover the remaining funds and strengthen protocol integrity.
“We are committed to compensating affected users once the investigation concludes,” a Cetus spokesperson said.
The Sui Foundation has also pledged additional security resources to audit all major protocols running on its blockchain.
Lessons for the DeFi Ecosystem
The Cetus hack serves as a wake-up call for DeFi protocols and investors alike.
Smart contract bugs continue to pose the biggest threat to user funds.
Transparent post-mortems and proactive coordination are now essential to maintain trust in decentralized finance.

