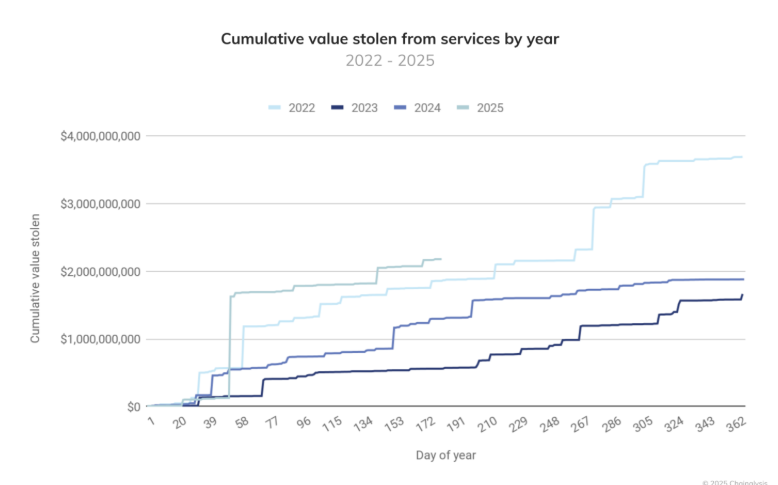
Centralized cryptocurrency exchanges (CEXs) remain top targets for hackers despite ongoing improvements in cybersecurity. A single breach can cause massive financial losses, user attrition, and reputational damage. According to Chainalysis, over $2.17 billion has already been stolen from crypto services in 2025, surpassing the entire 2024 figure by mid-year.
Such numbers highlight why crisis management for CEX is just as important as technical security. Without preparation, breaches can spiral into public panic and regulatory pressure, often more damaging than the attack itself.
Why CEX Crisis Management Must Go Beyond IT Fixes
While strong cyber defenses are critical, managing an exchange breach is not only about firewalls and patches. It’s about managing people and information flow.
- Users demand quick, transparent updates.
- Regulators expect compliance and professionalism.
- Employees need clear direction.
- Media amplifies every mistake.
Delayed or unclear communication often worsens the crisis. As experts explain, “What you say and how you say it matter as much as what you do.”
A Four-Part Cybersecurity Crisis Plan for CEXs
To prepare effectively, exchanges can follow a four-part framework:
1. Pre-crisis audits and risk assessments
- Identify gaps in processes and escalation chains.
- Define who communicates what in case of a hack.
- Clarify roles for technical, legal, PR, and compliance teams.
2. Exchange crisis simulations
- Conduct tabletop exercises that simulate a real hack.
- Test workflows, decision-making, and communication.
- Build internal confidence to act fast under pressure.
3. Real-time incident support
- Establish a central war room for crisis coordination.
- Align PR, legal, and customer support before issuing updates.
- Focus on facts only—avoid speculation.
4. Post-breach communication plan
- Keep users informed of ongoing fixes and upgrades.
- Publish a post-mortem report to restore credibility.
- Show transparency to rebuild user trust.
Habits That Set Top Exchanges Apart
Crisis-ready CEXs don’t wait for trouble—they prepare early. Leading platforms:
- Maintain simple, tested playbooks.
- Run regular training and breach drills.
- Treat crisis communication as strategic, not reactive.
Handled poorly, breaches can invite regulatory penalties, user migration, and brand collapse. Handled well, they can strengthen user confidence and market resilience.
Key Takeaways for Web3 Teams
- You don’t need a perfect plan—you need a tested one.
- Crisis response is company-wide: security, legal, comms, and leadership must work together.
- Run simulations regularly to catch blind spots.
- Transparent communication protects trust better than silence.
- Preparation is cheaper than recovery.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.