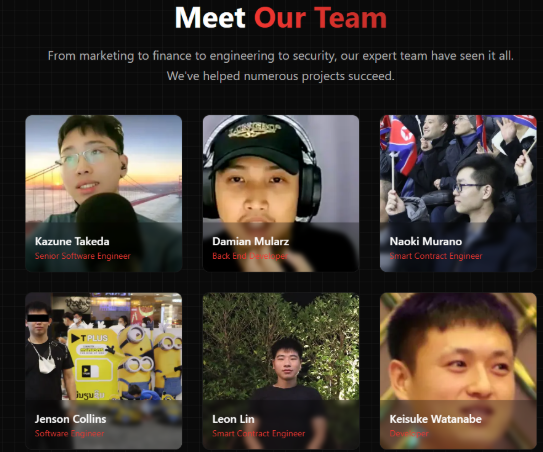
North Korean Hackers Targeting Crypto Firms
North Korean hacking groups are intensifying their attempts to infiltrate the cryptocurrency sector by posing as IT workers, according to Binance co-founder Changpeng “CZ” Zhao and the Security Alliance (SEAL) team. The ethical hacker group revealed profiles of at least 60 impersonators using fake names, GitHub accounts, and fraudulent credentials to secure employment in crypto firms.
CZ warned that these operatives pose as job candidates to gain access to sensitive positions in development, security, and finance. Once inside, they attempt to compromise company systems through malware-laden files, phishing links, or bribery of existing employees.
“They pose as job candidates to get jobs in your company. This gives them a ‘foot in the door’,” Zhao said, adding that some attackers even pose as employers to trick staff into installing malicious updates.
SEAL Team Repository Exposes Fake Identities
The SEAL white hat group, led by well-known security researcher Samczsun, compiled a repository of impersonators that includes:
- Fake names, aliases, and email addresses
- Citizenship and location details (both real and fake)
- GitHub repositories and coding samples
- Firms that unknowingly hired these agents
The SEAL database is designed to help crypto firms screen applicants and protect against infiltration attempts. In June, four North Korean operatives infiltrated multiple startups as freelance developers, stealing $900,000 collectively.
A Pattern of High-Profile Hacks
North Korean state-linked hackers, particularly the Lazarus Group, are suspected of being behind some of the largest crypto heists in history, including the $1.4 billion Bybit hack.
These cyberattacks have cost the industry billions, with hackers often using stolen funds to bypass sanctions and fund the country’s weapons programs.
Industry Response: Stronger Security Measures
Following the revelations, Coinbase CEO Brian Armstrong announced stricter internal controls, including:
- Mandatory in-person training in the US
- Citizenship verification and fingerprinting for staff with access to sensitive systems
Armstrong stressed the scale of the problem, noting that hundreds of North Korean agents appear to be trained every quarter specifically to target crypto companies.
The SEAL team’s findings underline the urgent need for crypto firms to strengthen employee vetting processes and educate staff on social engineering threats.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.