The U.S. Department of Justice (DOJ) has formally charged four North Korean nationals for orchestrating a nearly $1 million cryptocurrency theft by posing as remote blockchain developers. The individuals allegedly used false identities and fraudulent documentation to infiltrate U.S. and Serbian tech companies between 2020 and 2021.
North Korean Operatives Used Fake IDs to Infiltrate Blockchain Firms
The defendants — Kim Kwang Jin, Kang Tae Bok, Jong Pong Ju, and Chang Nam Il — reportedly operated under stolen and fabricated identities to hide their North Korean citizenship. They initially worked from the United Arab Emirates, then secured remote IT positions at a Georgia-based blockchain startup and a Serbian virtual token company.
The DOJ described the scheme as a “unique threat” to companies hiring remote IT workers, as attackers can bypass traditional background checks.
Over $915,000 in Crypto Stolen and Laundered
The indictment details two major thefts:
- In February 2022, Jong siphoned $175,000 in cryptocurrency.
- In March 2022, Kim exploited smart contract source code to steal $740,000 more.
The total stolen amounted to approximately $915,000, laundered through crypto mixers and shell accounts registered under fraudulent Malaysian IDs.
Stolen Funds Linked to North Korea’s Illicit Weapons Programs
According to prosecutors, the stolen assets were used to fund North Korea’s sanctioned activities, including its weapons development programs. The DOJ emphasized that this case is part of its DPRK RevGen: Domestic Enabler Initiative, launched in 2024 to disrupt North Korean revenue operations via U.S. channels.
“These operations are designed to bypass sanctions and funnel stolen money to the North Korean regime,” said DOJ national security officials.
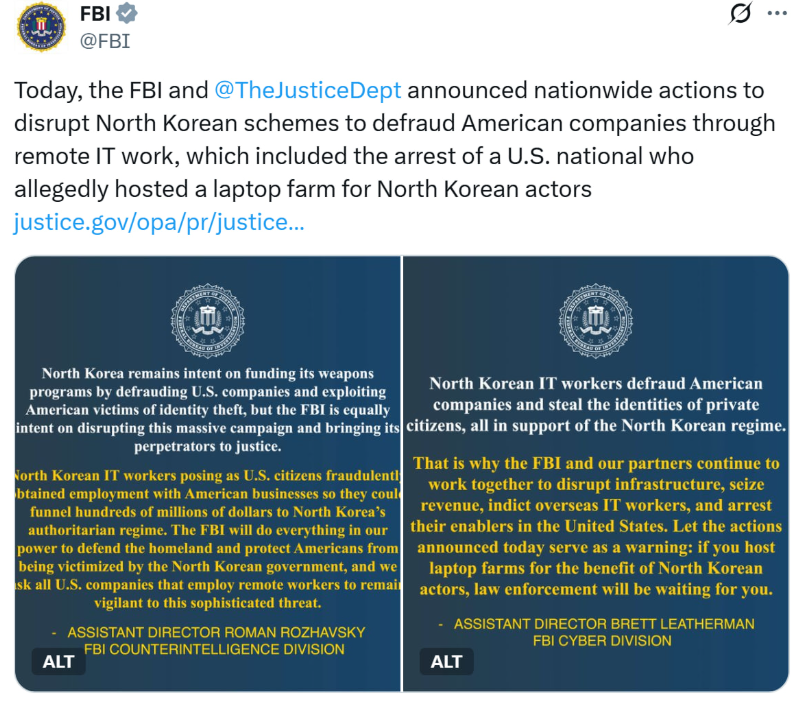
Wider Crackdown on North Korea’s Global Cyber Schemes
The case follows a broader DOJ investigation targeting North Korean cybercrime and fraud:
- Raids in 16 states uncovered over 200 devices and 30 financial accounts linked to fake job applicants.
- North Korean IT workers used fake U.S. identities to infiltrate over 100 American companies.
- In June, the DOJ filed a civil forfeiture complaint for $7.74 million in crypto connected to similar fraud schemes.
Outlook
This case highlights a growing threat from state-sponsored cybercrime exploiting remote work and decentralized finance. As blockchain firms expand globally, authorities are urging companies to strengthen identity verification, especially when hiring remote developers with access to sensitive code or funds.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.

