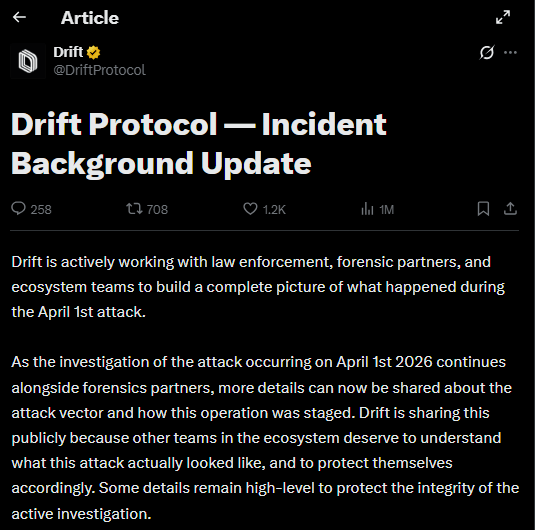
Drift Protocol has released preliminary findings of its investigation into the $285 million theft that occurred on April 1, 2026. The investigation indicates that the attack was a long term, organized infiltration operation lasting approximately six months.
Since fall 2025, attackers posed as a quantitative trading firm, engaging Drift team members at multiple international crypto conferences. Over this period, they compromised devices through code repository links and a TestFlight application, establishing trust with contributors by investing over $1 million of their own capital and conducting detailed discussions on trading strategies and vault integrations.
Attack Vectors and Methodology
Drift’s forensic analysis identifies three potential attack vectors:
- Code repository compromise – exploiting known VSCode and Cursor vulnerabilities from December 2025 to February 2026, allowing silent execution of malicious code.
- TestFlight application – downloaded under the guise of a wallet product.
- Other targeted interactions – meticulously staged over months, including in-person meetings at conferences.
All remaining protocol functions have been frozen, compromised wallets removed from the multisig, and attacker wallets flagged across exchanges and bridges.
Possible DPRK-Linked Attribution
Preliminary evidence, supported by the SEALS 911 team, links the operation to the same actors behind the October 2024 Radiant Capital hack, associated with UNC4736, a North Korean state-affiliated group also tracked as AppleJeus or Citrine Sleet. Operational overlaps and on-chain fund flows suggest medium-high confidence, although Mandiant has not formally attributed the exploit, pending full device forensics.
Community Guidance and Ongoing Investigation
Drift emphasized that the in-person attackers were not North Korean nationals but third-party intermediaries used for relationship building and infiltration. The investigation highlights the sophisticated, professional identities built by the attackers, including employment histories and public credentials.
Drift urges ecosystem teams to audit access, secure devices, and monitor for similar threats. For assistance, the team recommends reaching out to @SEAL911. Drift also thanked experts @tayvano_, @tanuki42_, @pcaversaccio, and @bax1337 for their contributions to the investigation.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.

