Cybercriminal group linked to former BlackCat operation targets healthcare and critical services
A rising ransomware group known as Embargo has moved more than $34 million in cryptocurrency from ransom payments since April 2024, according to blockchain intelligence firm TRM Labs. The group has primarily struck hospitals, pharmaceutical networks, and other critical infrastructure across the United States, raising concerns among cybersecurity experts.
Operating under a ransomware-as-a-service (RaaS) model, Embargo reportedly demanded up to $1.3 million per victim, with confirmed attacks on American Associated Pharmacies, Memorial Hospital and Manor in Georgia, and Weiser Memorial Hospital in Idaho.
“Embargo’s methods suggest an advanced operational structure, with laundering strategies designed to evade detection for months, if not years,” noted a TRM Labs analyst.
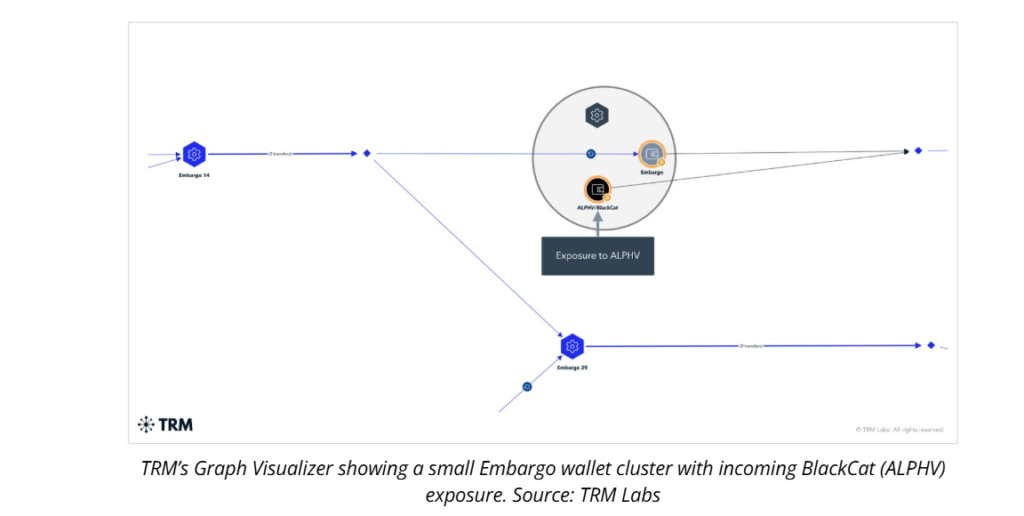
Investigators believe Embargo could be a rebranded version of the dismantled BlackCat (ALPHV) ransomware group, which vanished earlier this year amid allegations of an exit scam. TRM Labs identified technical overlaps between the two, including shared use of the Rust programming language, mirrored data leak site structures, and linked wallet infrastructure.
Currently, $18.8 million of Embargo’s crypto proceeds sit dormant in unaffiliated wallets—an apparent tactic to either wait out law enforcement scrutiny or move funds under more favorable laundering conditions later.
Laundering Network and High-Risk Platforms
TRM traced at least $13.5 million across various virtual asset service providers from May to August, with over $1 million routed through sanctioned exchange Cryptex.net. Experts say the group relies on intermediary wallets, high-risk exchanges, and sanctioned platforms to mask fund origins.
“While not as publicly aggressive as groups like LockBit, Embargo’s selective targeting makes it just as dangerous,” warned cybersecurity consultants.
The UK government is preparing to ban ransomware payments across public sector bodies and critical national infrastructure operators, such as energy, healthcare, and local councils. Under the proposal, victims outside the ban must report any intended ransom payment within 72 hours and provide a detailed incident report within 28 days.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.