Cybercrime group “GreedyBear” has stolen over $1 million in cryptocurrency using a massive network of fake browser extensions, malware, and scam websites, according to a new report by cybersecurity firm Koi Security.
Tuval Admoni, a lead researcher at Koi Security, said Thursday that GreedyBear is “redefining industrial-scale crypto theft.”
“Most groups pick a lane — maybe they do browser extensions, or they focus on ransomware… GreedyBear said, ‘Why not all three?’ And it worked. Spectacularly,” Admoni explained.
The group published over 150 malicious browser extensions on Firefox, impersonating popular crypto wallets such as MetaMask, TronLink, Exodus, and Rabby Wallet. These extensions are created using a technique called “Extension Hollowing” — first uploading a clean version to pass security checks, then later pushing malware-laced updates.
“This approach bypasses marketplace security while weaponizing user trust,” Admoni added.
Deddy Lavid, CEO of Cyvers, warned that browser extension stores are being exploited to clone wallet plugins, inflate reviews, and silently inject credential-stealing malware.
Nearly 500 Malware Samples Linked to Crypto Attacks
Beyond browser extensions, GreedyBear has distributed nearly 500 malware variants, targeting crypto wallets through credential stealers like LummaStealer and ransomware tools such as Luca Stealer.
Most malware samples were spread through Russian-language websites offering pirated software, suggesting potential ties to Russian threat actors.
Network of Sophisticated Scam Sites
The third prong of GreedyBear’s operation is a coordinated network of scam websites posing as legitimate crypto products — including wallets, hardware devices, and wallet recovery tools. These aren’t typical phishing pages; they are fully designed product pages created to build trust and lure victims.
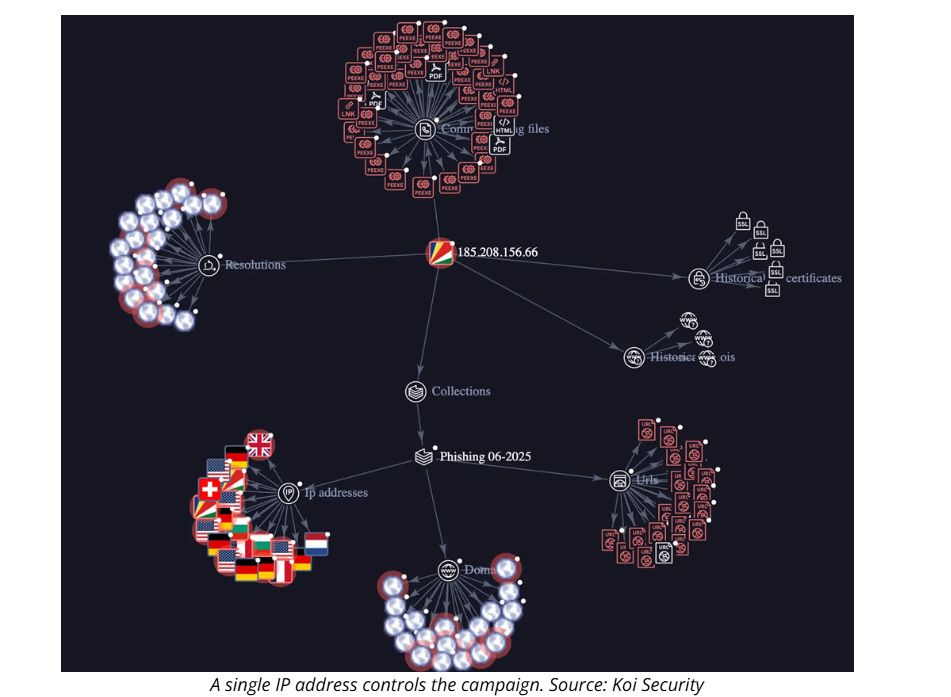
“One server coordinates all activities — credential theft, ransomware, and scam operations — giving them operational efficiency,” Admoni said.
GreedyBear’s campaign marks a dangerous evolution in crypto crime, showing how cybercriminals are scaling attacks by combining social engineering, malware, and supply chain infiltration.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.