$250K Exploit Sparks 99% Plunge in HAI Token
Cybersecurity firm Hacken suffered a major blow this weekend after a private key leak allowed a hacker to mint and dump $250,000 worth of Hacken Token (HAI). The exploit triggered a 99% collapse in the token’s price — from $0.015 to as low as $0.000056. HAI is now trading at $0.00026, far below its prior valuation.
How the Attack Happened
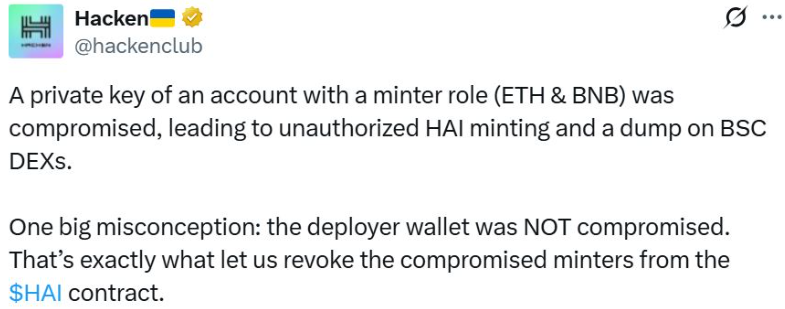
In an official post on X, Hacken revealed that the leaked private key was tied to a minting account on both Ethereum and BNB Chain. This access enabled the attacker to illegitimately create and sell massive amounts of HAI on decentralized exchanges. The token contract’s minting privileges have since been revoked, and the compromised wallet neutralized.
“There is currently no evidence of any compromise beyond the private keys,” the firm emphasized, noting that its core cybersecurity infrastructure remains unaffected.
Bridge Weakness the Root Cause
The vulnerability was introduced during architectural changes to Hacken’s blockchain bridge, which ironically were aimed at enhancing security and reducing risks. Hacken admitted the existing bridge was outdated, having been designed in an earlier market era, and was undergoing restructuring.
As a safety measure, all bridge transactions on Ethereum and BNB Chain have been paused. The company also warned the community about scam airdrop posts, confirming no airdrops are planned.
Tokens Bought Post-Hack Won’t Be Supported
In a significant update, Hacken CEO Dyma Budorin stated that HAI tokens bought after the hack will not be recognized in the forthcoming tokenomics. The firm aims to convert HAI into a regulated security token, blending equity ownership with blockchain flexibility.
“Now is the time to accelerate the idea implementation,” Budorin noted, referring to merging HAI utility with Hacken’s equity structure.
Recovery and Way Forward
Hacken has reassured users that all legitimate HAI balances remain traceable, and a swap mechanism for affected tokens will be introduced soon. Details on the transition to new tokenomics will follow.
This incident adds to a troubling trend: $1.63 billion in crypto has been stolen in Q1 2025 alone, according to PeckShield. Similar exploits — like Meta Pool’s minting vulnerability — highlight ongoing weaknesses in DeFi infrastructure, especially around token permissions and bridge security.
Conclusion
The Hacken token exploit marks another stark reminder of how even security-focused firms remain vulnerable to smart contract and key management flaws. While the company moves toward a regulated and equity-based token model, restoring trust in the ecosystem will be the biggest challenge moving forward.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.