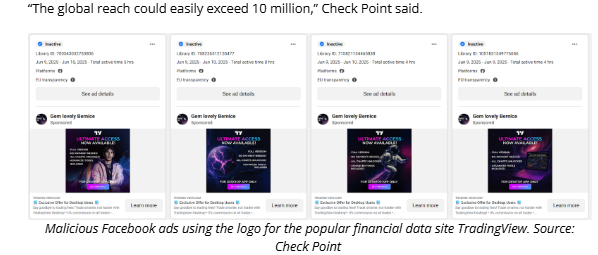
A new wave of malware-infested fake crypto apps has potentially exposed over 10 million users worldwide, with cybersecurity researchers warning investors and traders to stay alert.
Fake Crypto Apps Masquerade as Trusted Platforms
Since early 2024, a highly sophisticated malware campaign has been targeting crypto users through malicious advertisements. These ads mimic popular crypto trading platforms and wallets, luring victims to download apps that appear legitimate but are embedded with code designed to steal crypto assets and sensitive login credentials.
Over 35,000 fake ads have been detected across social media platforms, particularly in regions with high digital activity like Europe and Asia. The malware campaign, known for its stealth, uses advanced obfuscation to bypass detection by most antivirus tools.
JavaScript Malware Harvests Passwords and Wallet Data
The malware operates using JavaScript-based scripts that run in the background without requiring any input from the user. Once installed, the fake app redirects the victim to a real trading interface while silently extracting:
- Keyboard inputs (potential passwords)
- Auto-filled login credentials
- Telegram session data
- Browser cookies and history
- Control over crypto browser extensions like MetaMask
This dual-interface method makes it extremely difficult to detect, even for cybersecurity professionals.
Anti-Evasion Tactics Reduce Detection Rates
The campaign’s success stems from its “unique anti-evasion methods”, where both the fake app and the legitimate-looking interface load simultaneously. This allows attackers to collect data while maintaining the illusion of authenticity.
According to researchers, the malware’s obfuscation and use of compiled code make reverse engineering time-consuming and complex, further delaying global threat response.
How to Stay Safe from Crypto Malware Attacks
Users are urged to only download apps from verified sources, such as official app stores or direct links from trusted crypto platforms. Installing real-time anti-malware software that can detect JavaScript exploits is also recommended.
Crypto theft through malware is often irreversible, and stolen funds are rarely recovered due to blockchain anonymity. As the threat landscape evolves, user vigilance remains the first line of defense.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.