
Photo: Illustrative
Hackers Use Fake Google Play Pages to Spread Crypto Mining and Banking Malware
Hackers are running a phishing campaign that uses counterfeit Google Play Store pages to distribute malicious Android apps, primarily targeting users in Brazil. The fake pages closely resemble official Play Store layouts and promote apps such as “INSS Reembolso,” falsely presented as connected to Brazil’s social security services. Once installed, the app secretly loads hidden code in multiple stages, allowing attackers to gain remote access and maintain control of infected devices.
.jpeg)
Hackers are running a phishing campaign that uses counterfeit Google Play Store pages to distribute malicious Android apps, primarily targeting users in Brazil. The fake pages closely resemble official Play Store layouts and promote apps such as “INSS Reembolso,” falsely presented as connected to Brazil’s social security services. Once installed, the app secretly loads hidden code in multiple stages, allowing attackers to gain remote access and maintain control of infected devices.
Crypto Mining Malware Turns Phones Into Mining Machines
After installation, the malware downloads a crypto mining payload based on XMRig designed for ARM devices. The malicious software silently connects infected smartphones to attacker-controlled mining servers. It monitors battery levels, device temperature, and user activity to adjust mining operations and remain undetected, while looping silent audio to bypass Android background restrictions.
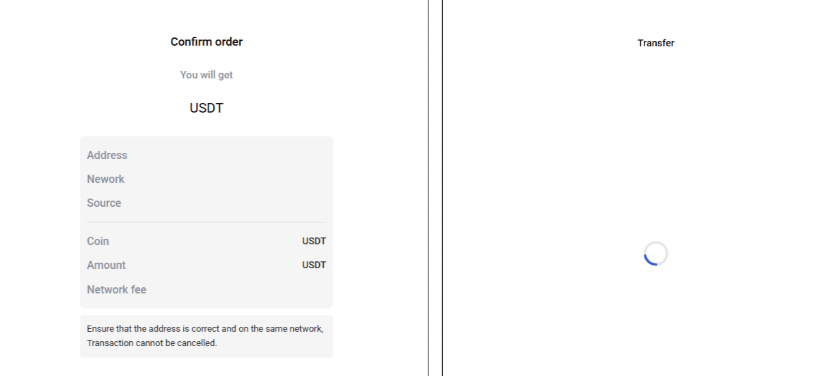
Banking Trojan Targets USDT Wallet Transfers
Some variants also install a banking Trojan that targets Binance and Trust Wallet users, especially during USDT transactions. The malware overlays fake screens and replaces wallet addresses, enabling attackers to redirect funds without users noticing.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.
Live market reaction
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.
Start trading
with BloFin today
Up to $500 sign-up bonus and zero-fee trading on your first 30 days.
Buy crypto nowⓘ You will be redirected to BloFin
About the author
.jpeg)
Emerging voice in crypto journalism with a background in fintech and digital economics. Covers DeFi, NFTs, and the evolving regulatory landscape.
BitMine Expands Ethereum Holdings With $238M Purchase, Nears 5% Supply Target
Bitcoin Price Outlook: Why BTC Could Move Toward $95K After $80K Recovery
Trump-Linked World Liberty Files Defamation Case Against Justin Sun Over WLFI Token Dispute


