
Photo: Illustrative
Lazarus Group Expands Cyber Threat With New ‘Mach-O Man’ Malware Targeting Crypto Firms
North Korea’s Lazarus Group has introduced a new macOS-focused cyberattack campaign known as “Mach-O Man,” significantly increasing risks for executives in fintech, cryptocurrency and other high-value industries. Security researchers warn that the group, responsible for an estimated $6.7 billion in stolen funds since 2017, is intensifying its operations with highly targeted social engineering tactics.

North Korea’s Lazarus Group has introduced a new macOS-focused cyberattack campaign known as “Mach-O Man,” significantly increasing risks for executives in fintech, cryptocurrency and other high-value industries. Security researchers warn that the group, responsible for an estimated $6.7 billion in stolen funds since 2017, is intensifying its operations with highly targeted social engineering tactics.
According to blockchain security researcher Natalie Newson, the group has remained highly active, siphoning more than $500 million from recent exploits involving Drift and KelpDAO over the past two weeks. She described the campaign as a state-directed financial operation rather than isolated criminal activity, highlighting its scale and speed.
ClickFix Technique Turns Routine Meetings Into Security Breaches
The Mach-O Man malware relies on a social engineering method called ClickFix, which tricks victims into joining fake online meetings hosted through common communication tools. Victims receive urgent meeting invitations that lead to convincing fake websites instructing them to paste a command into their Mac terminal to resolve an apparent connection issue.
Once executed, the command grants attackers direct access to corporate systems, software platforms and financial assets. Researchers note that the malware often deletes itself after deployment, making detection difficult and leaving victims unaware until losses occur.
Modular Malware Expands Risk Across Cybercrime Networks
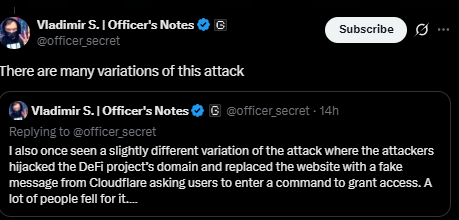
Experts warn that Mach-O Man is a modular malware kit originally created by Lazarus Group’s Chollima division but now used by other cybercriminal organizations. Some reported incidents include attackers hijacking decentralized finance project domains and replacing legitimate pages with fake verification messages designed to capture access credentials.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.
Live market reaction
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.
Start trading
with BloFin today
Up to $500 sign-up bonus and zero-fee trading on your first 30 days.
Buy crypto nowⓘ You will be redirected to BloFin
About the author

8+ years covering crypto markets, macro, and geopolitics. Previously at Decrypt and CoinDesk. Focused on the intersection of digital assets and traditional finance.
BitMine Expands Ethereum Holdings With $238M Purchase, Nears 5% Supply Target
Bitcoin Price Outlook: Why BTC Could Move Toward $95K After $80K Recovery
Trump-Linked World Liberty Files Defamation Case Against Justin Sun Over WLFI Token Dispute


