
Photo: Illustrative
North Korean Hackers Used AI-Driven Social Engineering in Zerion Crypto Attack
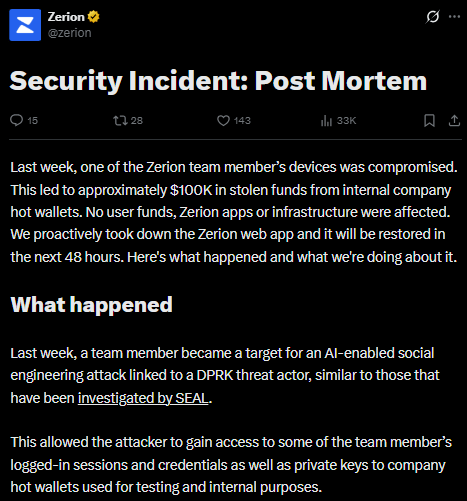
Crypto wallet platform Zerion has confirmed that North Korean linked hackers used AI-assisted social engineering techniques to steal around $100,000 from its corporate hot wallets. The company released a post-mortem report stating that no user funds, apps, or core infrastructure were impacted, although the web application was temporarily disabled as a precaution during the investigation.
.jpeg)
Crypto wallet platform Zerion has confirmed that North Korean linked hackers used AI-assisted social engineering techniques to steal around $100,000 from its corporate hot wallets. The company released a post-mortem report stating that no user funds, apps, or core infrastructure were impacted, although the web application was temporarily disabled as a precaution during the investigation.
The attack highlights how threat actors are increasingly targeting human systems rather than exploiting smart contract vulnerabilities. According to Zerion, the hackers gained access to logged-in team sessions, credentials, and private keys associated with company wallets.
AI-Enabled Social Engineering Becoming a Key Cybersecurity Threat
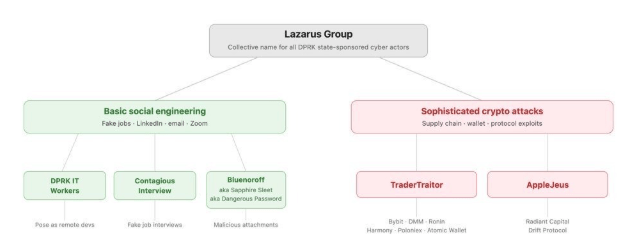
This incident marks the second major social-engineering-based crypto attack this month, following a $280 million exploit of Drift Protocol, which was also linked to North Korean actors. Security researchers note that these operations rely heavily on long-term deception strategies rather than technical exploits.
Groups such as UNC1069 have been observed running multi-week campaigns across platforms like Telegram, LinkedIn, and Slack, often impersonating trusted contacts or compromised accounts to build credibility before executing attacks.
Growing Use of AI Expands Cyberattack Capabilities
Security experts warn that AI tools are now being used to enhance phishing, image manipulation, and impersonation tactics, making attacks more convincing and harder to detect. Reports from cybersecurity firms indicate that North Korean groups have been refining these methods for years, targeting developers, DeFi contributors, and crypto infrastructure workers as primary entry points into the ecosystem.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.
Live market reaction
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.
Start trading
with BloFin today
Up to $500 sign-up bonus and zero-fee trading on your first 30 days.
Buy crypto nowⓘ You will be redirected to BloFin
About the author
.jpeg)
Emerging voice in crypto journalism with a background in fintech and digital economics. Covers DeFi, NFTs, and the evolving regulatory landscape.
BitMine Expands Ethereum Holdings With $238M Purchase, Nears 5% Supply Target
Bitcoin Price Outlook: Why BTC Could Move Toward $95K After $80K Recovery
Trump-Linked World Liberty Files Defamation Case Against Justin Sun Over WLFI Token Dispute


