Bitcoin Security Relies on Elliptic Curve Cryptography
The security of Bitcoin depends on a cryptographic method known as Elliptic Curve Cryptography. Each Bitcoin wallet uses a private key a secret 256-bit number to generate a public key using a mathematical curve called secp256k1.
This system functions as a one-way mathematical process. While generating a public key from a private key is fast, reversing the process using classical computers is considered practically impossible. The difficulty of solving the elliptic curve discrete logarithm problem means that traditional machines would require more time than the age of the universe to determine a private key from a public key.
Shor’s Algorithm Presents a Breakthrough Risk
In 1994, mathematician Peter Shor introduced Shor’s Algorithm, a method capable of solving the discrete logarithm problem efficiently using quantum computing. Unlike classical systems, quantum computers use superposition, entanglement and interference to analyze many possible values simultaneously.
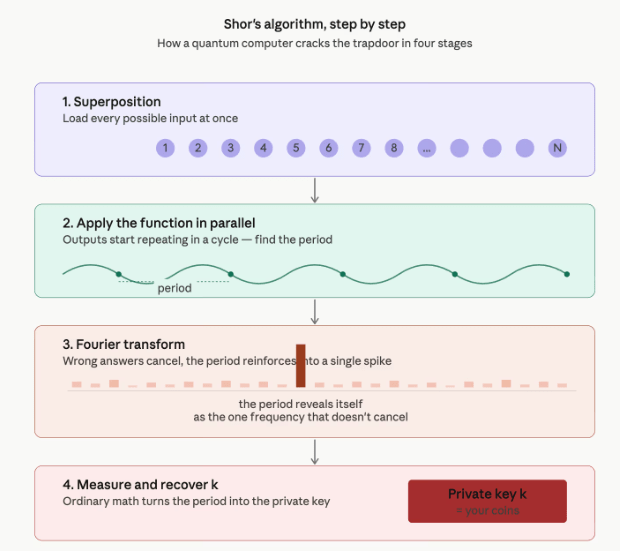
By identifying repeating mathematical patterns within elliptic curve operations, Shor’s Algorithm can determine the private key associated with a public key. Once recovered, the attacker could control the corresponding wallet and transfer funds without authorization.
Google Research Suggests a Nine-Minute Attack Window
A recent study from Google’s Quantum AI division, with contributions from researchers including Justin Drake and Dan Boneh, proposed a realistic attack model targeting Bitcoin encryption.
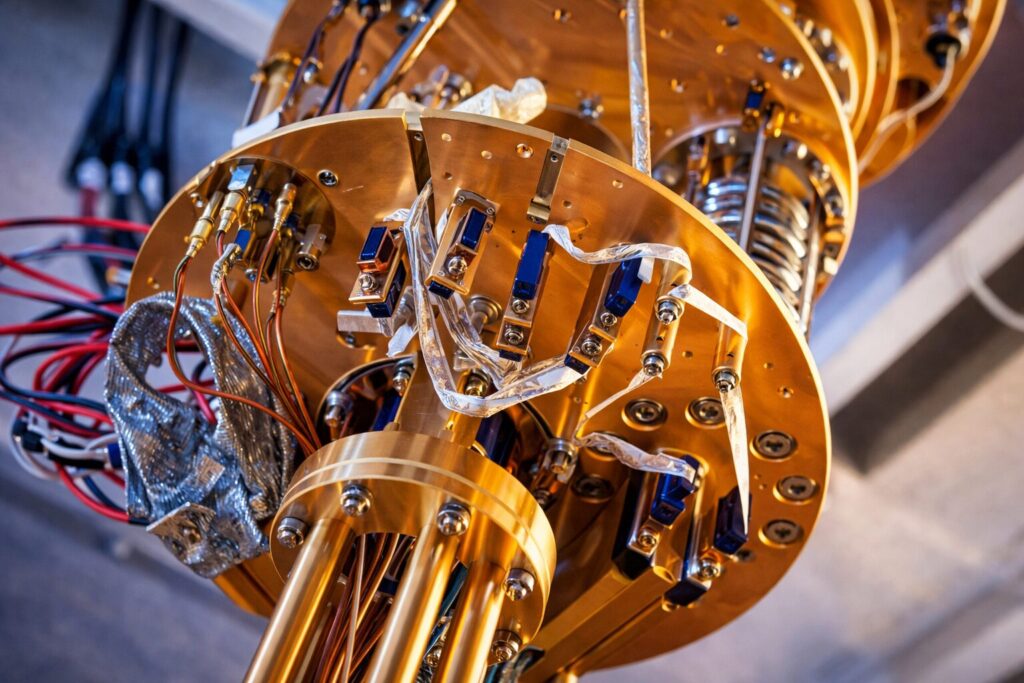
The research reduced previous hardware estimates from millions of qubits to fewer than 500,000 physical qubits, using around 1,200 to 1,450 logical qubits and tens of millions of Toffoli gates. The study also showed that much of the required computation could be completed in advance, allowing the final stage to finish in about nine minutes once a public key becomes visible.
Exposure Risk and Long-Term Implications
Bitcoin transactions typically confirm in roughly 10 minutes, creating a narrow window where attackers could attempt to intercept funds during broadcast. Researchers estimate attackers could have about a 41% chance of completing the calculation before confirmation.
A larger concern involves approximately 6.9 million bitcoin, nearly one-third of total supply, stored in wallets where public keys are already visible. These holdings could be targeted without time pressure if sufficiently advanced quantum hardware becomes available.
While such machines do not yet exist, the research highlights the growing importance of quantum-resistant cryptographic upgrades to secure long-term blockchain infrastructure.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.