Unauthorized Access to Internal Systems Impacts Limited Customer Data
Cloud deployment platform Vercel confirmed a security breach involving unauthorized access to portions of its internal infrastructure, affecting what the company described as a limited subset of customers. The company said external incident response teams have been engaged and law enforcement authorities notified, while services remain operational.
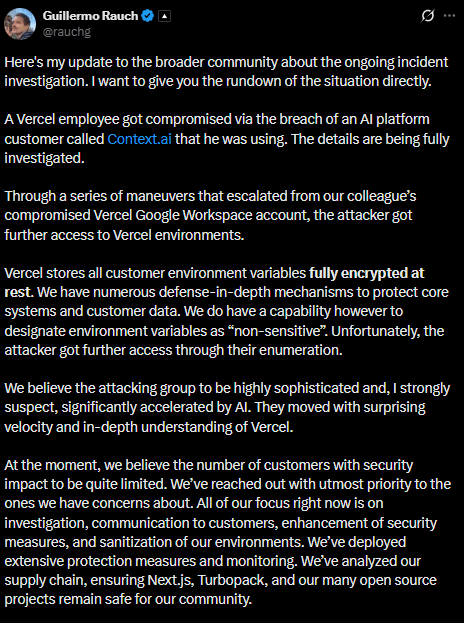
According to internal findings, the breach originated through a compromised account linked to a third-party AI tool identified as Context.ai. Attackers reportedly gained entry after exploiting a compromised Google Workspace OAuth connection, allowing them to escalate access within Vercel’s internal systems.
Vercel CEO Guillermo Rauch said on X;
Hacker Claims Stolen Data Including Tokens and Source Code
A threat actor operating under the name ShinyHunters posted on the cybercrime forum BreachForums offering alleged Vercel data for $2 million. The dataset reportedly includes access keys, internal deployment credentials, source code, and tokens associated with GitHub and NPM services. A sample shared online allegedly contained about 580 employee records, including email addresses and account details.
Developer Theo Browne, wrote on X;
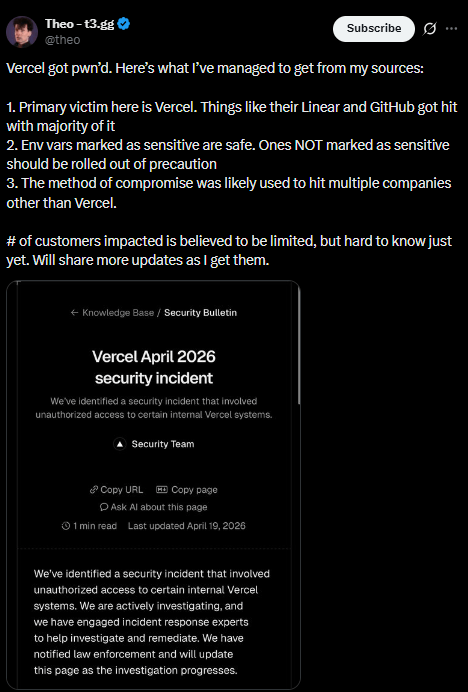
Security experts warned that many Web3 applications host interfaces on Vercel, meaning exposed environment variables labeled as non-sensitive could pose risks if not rotated immediately. The investigation remains ongoing as officials work to determine the full scope and potential impact on software deployments.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.

