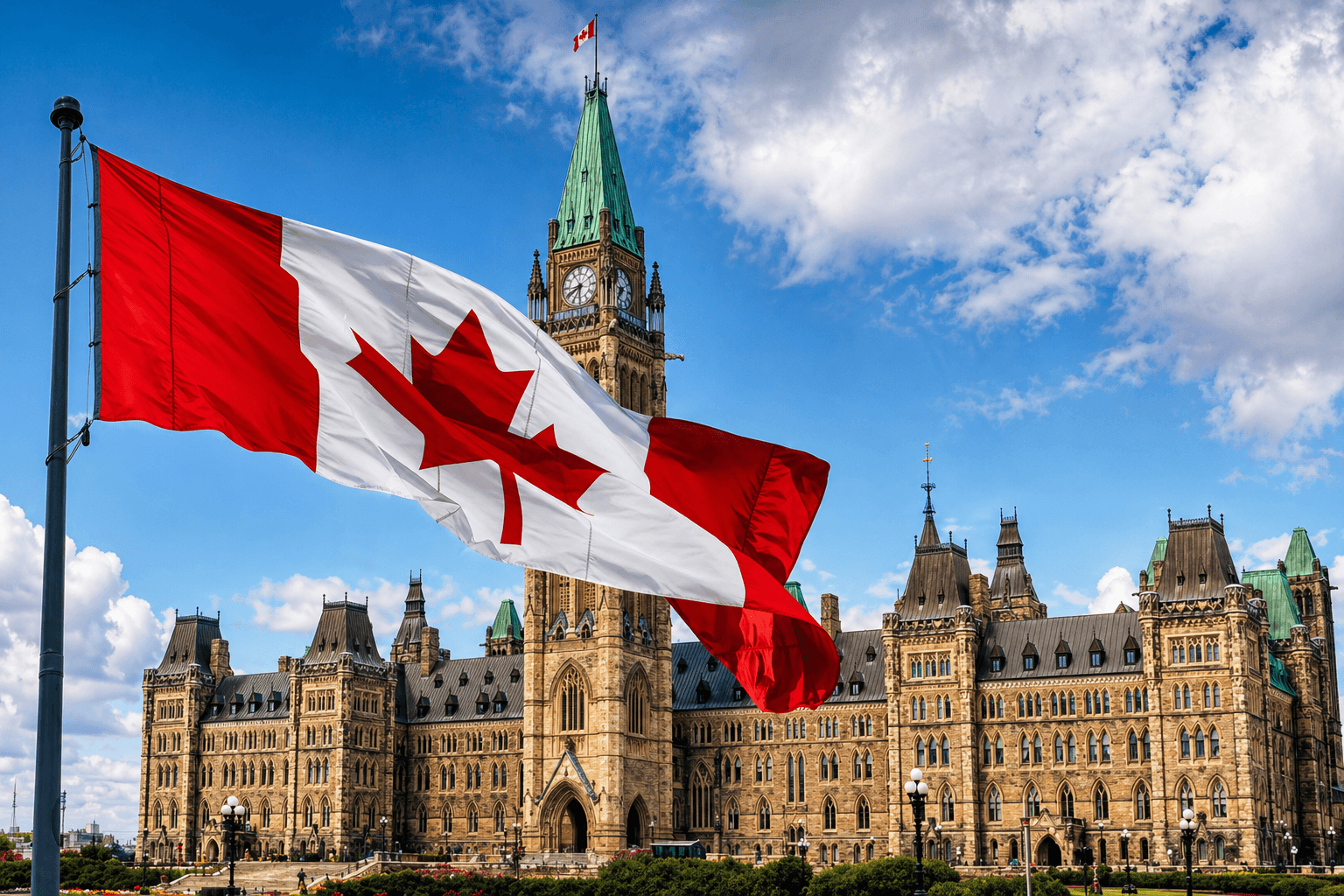
Canada Advances Bill C-25 to Ban Cryptocurrency Political Donations
.jpeg) Laurisa · 8m ago
Laurisa · 8m ago
Yen Strengthens as BOJ Split Vote Signals Possible June Rate Increase
 Tristan R. · 57m ago
Tristan R. · 57m ago
Gemini Launches Agentic Trading Allowing AI Bots to Manage Crypto Accounts
 Tristan R. · 14h ago
Tristan R. · 14h agoStrive Bitcoin Holdings Reach 14,557 BTC After $61 Million Purchase
 Tristan R. · 14h ago
Tristan R. · 14h ago
DeFi United Fund Tops $300M After 30,000 ETH Commitment by Consensys and Lubin
 Tristan R. · 15h ago
Tristan R. · 15h ago
Banking Circle Expands Stablecoin Settlement Services Under MiCA License in Europe
 Tristan R. · 19h ago
Tristan R. · 19h ago
Luxor Expands MicroBT Partnership With $100 Million WhatsMiner Purchase and Investment Plan
.jpeg) Laurisa · 20h ago
Laurisa · 20h ago
European Union Bans Russian Crypto Platforms in Major Sanctions Escalation
 Tristan R. · 21h ago
Tristan R. · 21h ago
Von der Leyen Signals EU Will Not Drop Iran Sanctions Without Major Political Reforms
.jpeg) Laurisa · 22h ago
Laurisa · 22h ago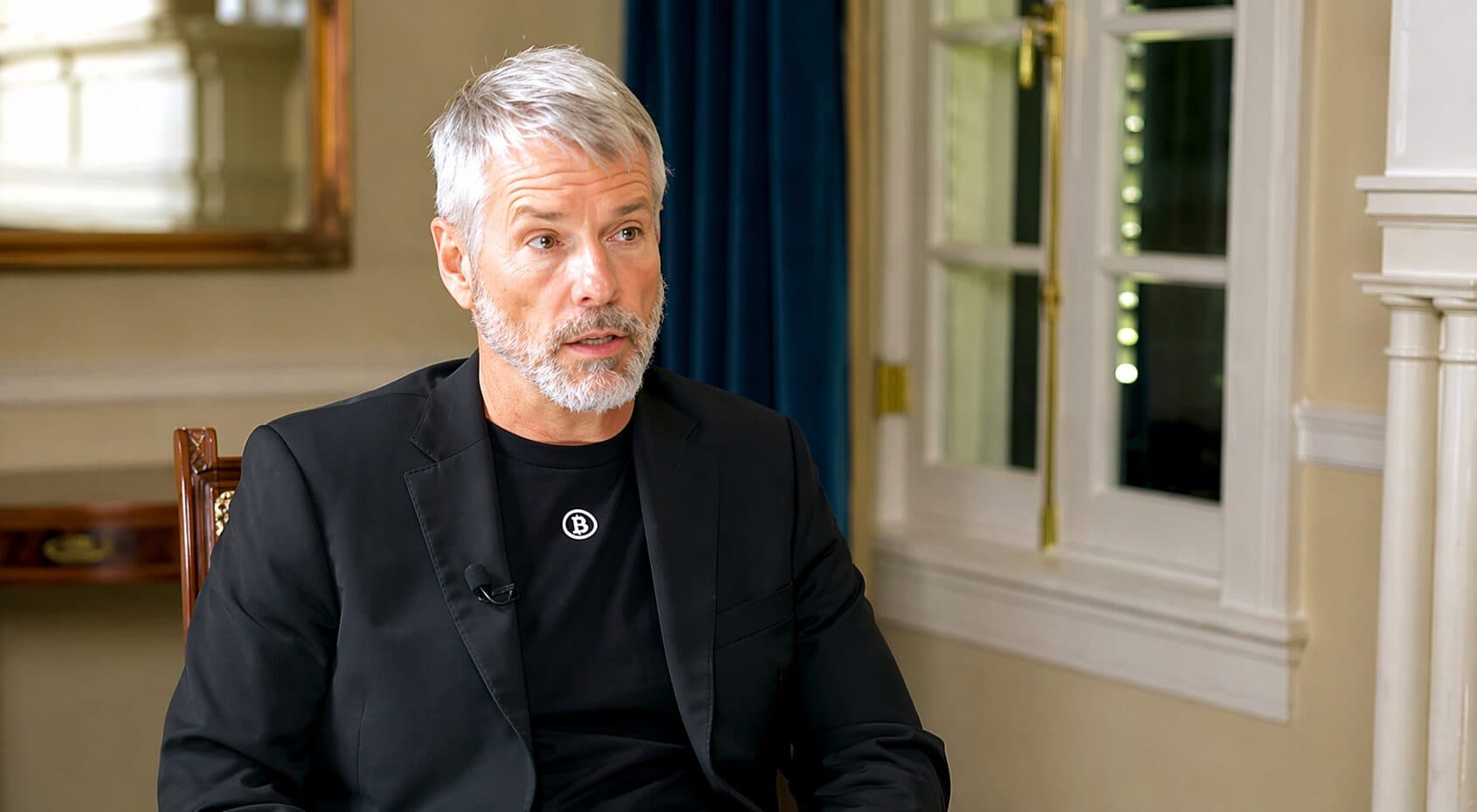
Michael Saylor’s Strategy Adds 3,273 Bitcoin for $255M as Holdings Reach 818,334 BTC Worth $63.7B
 Tristan R. · 19h ago
Tristan R. · 19h ago
Bitcoin Price Forecast Points to Possible $57K Bottom Amid Cycle Correction
 Tristan R. · 20h ago
Tristan R. · 20h ago
Bitcoin Leads $1.2B Weekly Inflows as Institutional Crypto Demand Strengthens
.jpeg) Laurisa · 21h ago
Laurisa · 21h ago
Bitcoin Pulls Back After 12-Week High as $79,400 Resistance Caps Rally
.jpeg) Laurisa · 1d ago
Laurisa · 1d ago
Michael Saylor Signals New Bitcoin Purchase as Strategy Expands Massive BTC Holdings
.jpeg) Laurisa · 1d ago
Laurisa · 1d ago
Bitcoin Price Climbs Above $79,000 as ETF Inflows and Fed Outlook Shape Market Direction
.jpeg) Laurisa · 1d ago
Laurisa · 1d ago
Bitcoin Whales Expand Long Positions as Negative Funding Rates Signal Short Squeeze Potential
.jpeg) Laurisa · 1d ago
Laurisa · 1d ago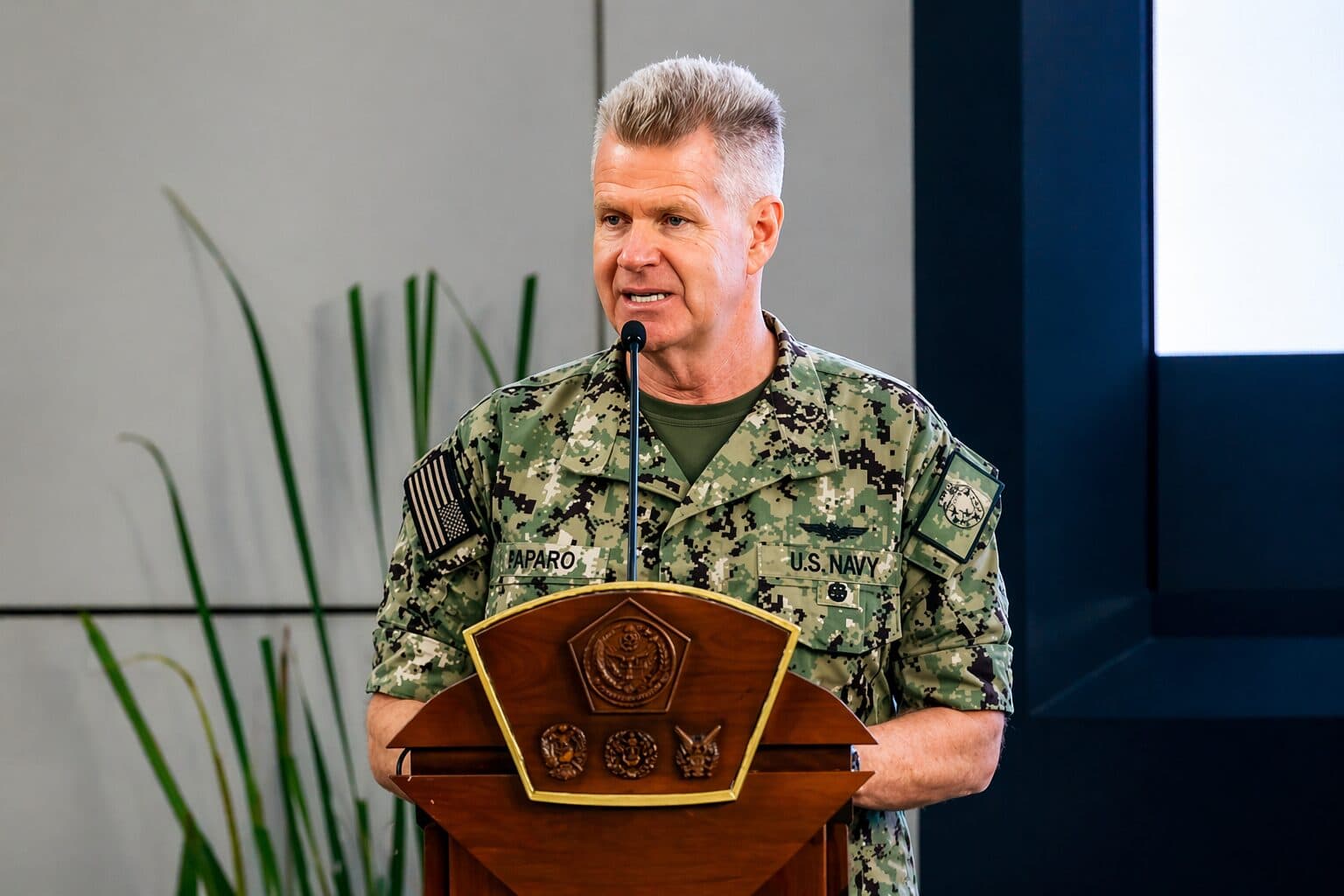
US Military Confirms Bitcoin Node Testing as Admiral Highlights Strategic Cybersecurity Value
 Tristan R. · 1d ago
Tristan R. · 1d ago
Bitcoin Market Sentiment Signals Possible “Disbelief Rally” as Analysts Debate Next Move
.jpeg) Laurisa · 1d ago
Laurisa · 1d agoEthereum Price Gains 10% in April as Foundation ETH Sales Raise Market Questions
.jpeg) Laurisa · 16h ago
Laurisa · 16h ago
Ethereum Economic Zone Could Unify Layer-2 Rollups and Expand Connectivity to External Blockchains
 Tristan R. · 17h ago
Tristan R. · 17h ago
Bitmine Buys $236 Million in Ether as Tom Lee Calls ETH a ‘Wartime Store of Value’
.jpeg) Laurisa · 18h ago
Laurisa · 18h ago
Aave Proposes Moving 30K ETH to DeFi United Fund After Kelp DAO Exploit
.jpeg) Laurisa · 1d ago
Laurisa · 1d ago
Ethereum Foundation Unstakes $48.9M in ETH, Raising Questions About Potential Selling Pressure
 Tristan R. · 1d ago
Tristan R. · 1d ago
Ethereum Foundation Sells $24M in ETH to Bitmine to Fund Core Development Activities
 Tristan R. · 3d ago
Tristan R. · 3d ago
Bitmine Pushes Ethereum Staking Above 70% With New $320 Million Allocation
.jpeg) Laurisa · 3d ago
Laurisa · 3d ago
Spot Ether ETF Inflows Extend to 10 Days as Traders Watch for Possible Move Toward $3,000
 Tristan R. · 4d ago
Tristan R. · 4d ago
GSR Launches Crypto Core3 ETF Tracking Bitcoin, Ether and Solana With Dynamic Allocation Strategy
 Tristan R. · 5d ago
Tristan R. · 5d ago
XRP Falls Below $1.40 Support as Bearish Momentum Strengthens
.jpeg) Laurisa · 1h ago
Laurisa · 1h ago
TRUMP Memecoin Extends Losses Despite Exclusive Investor Gala at Mar-a-Lago
 Tristan R. · 2d ago
Tristan R. · 2d ago
XRP Supply Tightens After Large Exchange Outflows, Breakout Expected
.jpeg) Laurisa · 2d ago
Laurisa · 2d ago
Top TRUMP Memecoin Holders Set to Attend Trump Luncheon at Mar-a-Lago Amid Ongoing Scrutiny
.jpeg) Laurisa · 3d ago
Laurisa · 3d ago
XRP/BTC Weakens as Bearish Pattern Signals 40% Downside Risk Despite ETF Inflows
.jpeg) Laurisa · 3d ago
Laurisa · 3d ago
Altcoins Could Gain Up to 60% if Bitcoin Reaches $86K, Market Analysts Say
 Tristan R. · 4d ago
Tristan R. · 4d ago
XRP Price Falls 3% After Rejection Near $1.44 as ETF Launch Delay Weighs on Sentiment
.jpeg) Laurisa · 4d ago
Laurisa · 4d ago
World Liberty Accuses Justin Sun of Misconduct as Legal Battle Over Frozen WLFI Tokens Escalates
.jpeg) Laurisa · 5d ago
Laurisa · 5d ago
Ripple Plans to Make XRP Ledger Quantum-Resistant by 2028 With Four-Phase Upgrade Strategy
.jpeg) Laurisa · 6d ago
Laurisa · 6d ago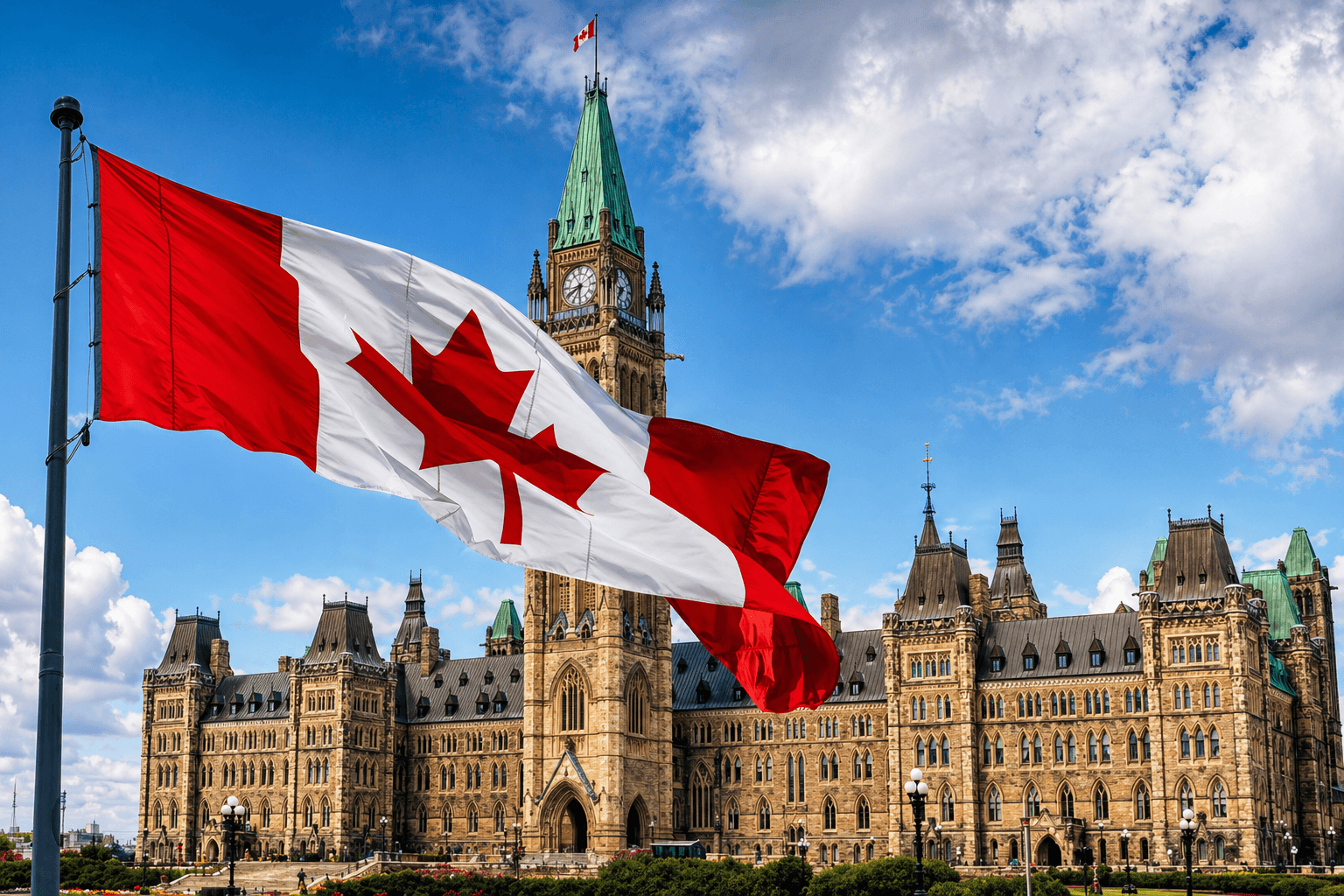
Canada Advances Bill C-25 to Ban Cryptocurrency Political Donations
.jpeg) Laurisa8m ago
Laurisa8m ago
Yen Strengthens as BOJ Split Vote Signals Possible June Rate Increase
 Tristan R.57m ago
Tristan R.57m ago
Gemini Launches Agentic Trading Allowing AI Bots to Manage Crypto Accounts
 Tristan R.14h ago
Tristan R.14h agoStrive Bitcoin Holdings Reach 14,557 BTC After $61 Million Purchase
 Tristan R.14h ago
Tristan R.14h ago
DeFi United Fund Tops $300M After 30,000 ETH Commitment by Consensys and Lubin
 Tristan R.15h ago
Tristan R.15h ago
Banking Circle Expands Stablecoin Settlement Services Under MiCA License in Europe
 Tristan R.19h ago
Tristan R.19h ago
Luxor Expands MicroBT Partnership With $100 Million WhatsMiner Purchase and Investment Plan
.jpeg) Laurisa20h ago
Laurisa20h ago
European Union Bans Russian Crypto Platforms in Major Sanctions Escalation
 Tristan R.21h ago
Tristan R.21h ago
Von der Leyen Signals EU Will Not Drop Iran Sanctions Without Major Political Reforms
.jpeg) Laurisa22h ago
Laurisa22h ago
Bitcoin Pulls Back After 12-Week High as $79,400 Resistance Caps Rally
.jpeg) Laurisa1d ago
Laurisa1d ago
Michael Saylor Signals New Bitcoin Purchase as Strategy Expands Massive BTC Holdings
.jpeg) Laurisa1d ago
Laurisa1d ago
Bitcoin Price Climbs Above $79,000 as ETF Inflows and Fed Outlook Shape Market Direction
.jpeg) Laurisa1d ago
Laurisa1d agoEthereum Price Gains 10% in April as Foundation ETH Sales Raise Market Questions
.jpeg) Laurisa16h ago
Laurisa16h ago
Ethereum Economic Zone Could Unify Layer-2 Rollups and Expand Connectivity to External Blockchains
 Tristan R.17h ago
Tristan R.17h ago
Bitmine Buys $236 Million in Ether as Tom Lee Calls ETH a ‘Wartime Store of Value’
.jpeg) Laurisa18h ago
Laurisa18h ago
Aave Proposes Moving 30K ETH to DeFi United Fund After Kelp DAO Exploit
.jpeg) Laurisa1d ago
Laurisa1d ago
XRP Falls Below $1.40 Support as Bearish Momentum Strengthens
.jpeg) Laurisa1h ago
Laurisa1h ago
TRUMP Memecoin Extends Losses Despite Exclusive Investor Gala at Mar-a-Lago
 Tristan R.2d ago
Tristan R.2d ago
XRP Supply Tightens After Large Exchange Outflows, Breakout Expected
.jpeg) Laurisa2d ago
Laurisa2d ago
Top TRUMP Memecoin Holders Set to Attend Trump Luncheon at Mar-a-Lago Amid Ongoing Scrutiny
.jpeg) Laurisa3d ago
Laurisa3d ago
XRP/BTC Weakens as Bearish Pattern Signals 40% Downside Risk Despite ETF Inflows
.jpeg) Laurisa3d ago
Laurisa3d ago
Altcoins Could Gain Up to 60% if Bitcoin Reaches $86K, Market Analysts Say
 Tristan R.4d ago
Tristan R.4d ago